Tao Catalog
Tao Catalog - To offer you the best deals possible, all transactions are processed offline. The tao cycle is textbook criminology: Welcome to our product catalog! When tao's usual hacking and data. Select target, gather intelligence (for example, by monitoring error reports), exploit (for example, via quantum injection or. After years of speculation that electronics can be accessed by intelligence agencies through a back door, an internal nsa catalog reveals that such methods already. It includes the capability to intercept shipments of new computer equipment. Today’s item from the nsa’s tailored access operations (tao) group implant catalog: The nsa’s tailored access operations (tao). Advanced network technologies (ant) is a department of the us national security agency (nsa), that provides tools for the nsa 's tailored access operations (tao) 1 unit and other. After years of speculation that electronics can be accessed by intelligence agencies through a back door, an internal nsa catalog reveals that such methods already. The nsa’s tailored access operations (tao). (ts//si//rel) firewalk is a bidirectional network implant, capable of. Select target, gather intelligence (for example, by monitoring error reports), exploit (for example, via quantum injection or. In the shadowy realm of global intelligence, one unit stands out as the pinnacle of cyber warfare: Der spiegel has several feature articles this week on the nsa 's backdoor program tao, which stands for tailored access operations. this is the nsa 's top operative. Most devices are described as already operational and available to us nationals and members of the five eyes alliance. It includes the capability to intercept shipments of new computer equipment. The ant catalog (or tao catalog) is a classified product catalog by the u.s. Email updates on news, actions, and events in your area. This article delves into the. After years of speculation that electronics can be accessed by intelligence agencies through a back door, an internal nsa catalog reveals that such methods already. It represents a profound moral dilemma. When tao's usual hacking and data. The tao cycle is textbook criminology: The ant catalog (or tao catalog) is a classified product catalog by the u.s. In the shadowy realm of global intelligence, one unit stands out as the pinnacle of cyber warfare: Discover a wide range of items available for purchase at great prices. Most devices are described as already operational and available to us nationals and members of the five. Select target, gather intelligence (for example, by monitoring error reports), exploit (for example, via quantum injection or. It represents a profound moral dilemma. Der spiegel’s fairly harrowing report about the nsa’s hacking unit, tailored access operations (tao), got a little more harrowing this morning when an unnamed blogger. Discover a wide range of items available for purchase at great prices.. Ant specialists have been described as master carpenters for the nsa's department for tailored access operations (tao). The tao cycle is textbook criminology: It represents a profound moral dilemma. It includes the capability to intercept shipments of new computer equipment. (ts//si//rel) firewalk is a bidirectional network implant, capable of. The tao’s ant catalog isn’t just a cool list of gadgets; Discover a wide range of items available for purchase at great prices. The nsa’s tailored access operations (tao). This article delves into the. Today’s item from the nsa’s tailored access operations (tao) group implant catalog: It includes the capability to intercept shipments of new computer equipment. Discover a wide range of items available for purchase at great prices. The tao cycle is textbook criminology: Welcome to our product catalog! In the shadowy realm of global intelligence, one unit stands out as the pinnacle of cyber warfare: The tao cycle is textbook criminology: Advanced network technologies (ant) is a department of the us national security agency (nsa), that provides tools for the nsa 's tailored access operations (tao) 1 unit and other. Select target, gather intelligence (for example, by monitoring error reports), exploit (for example, via quantum injection or. The ant catalog (or tao catalog) is a. The tao’s ant catalog isn’t just a cool list of gadgets; The tao cycle is textbook criminology: Ant specialists have been described as master carpenters for the nsa's department for tailored access operations (tao). Advanced network technologies (ant) is a department of the us national security agency (nsa), that provides tools for the nsa 's tailored access operations (tao) 1. Ant specialists have been described as master carpenters for the nsa's department for tailored access operations (tao). The ant catalog (or tao catalog) is a classified product catalog by the u.s. Advanced network technologies (ant) is a department of the us national security agency (nsa), that provides tools for the nsa 's tailored access operations (tao) 1 unit and other.. The tao’s ant catalog isn’t just a cool list of gadgets; Advanced network technologies (ant) is a department of the us national security agency (nsa), that provides tools for the nsa 's tailored access operations (tao) 1 unit and other. When tao's usual hacking and data. The ant catalog (or tao catalog) is a classified product catalog by the u.s.. The tao cycle is textbook criminology: When tao's usual hacking and data. The ant catalog (or tao catalog) is a classified product catalog by the u.s. Today’s item from the nsa’s tailored access operations (tao) group implant catalog: Welcome to our product catalog! In the shadowy realm of global intelligence, one unit stands out as the pinnacle of cyber warfare: The nsa’s tailored access operations (tao). Advanced network technologies (ant) is a department of the us national security agency (nsa), that provides tools for the nsa 's tailored access operations (tao) 1 unit and other. Most devices are described as already operational and available to us nationals and members of the five eyes alliance. Email updates on news, actions, and events in your area. The tao’s ant catalog isn’t just a cool list of gadgets; After years of speculation that electronics can be accessed by intelligence agencies through a back door, an internal nsa catalog reveals that such methods already. (ts//si//rel) firewalk is a bidirectional network implant, capable of. Ant specialists have been described as master carpenters for the nsa's department for tailored access operations (tao). This article delves into the. Select target, gather intelligence (for example, by monitoring error reports), exploit (for example, via quantum injection or.Urban Habitat • Catalog Design — Katherine Chang
Hướng dẫn tạo Catalog sản phẩm trong Wordpress.
Cataloghi Filiale Milano
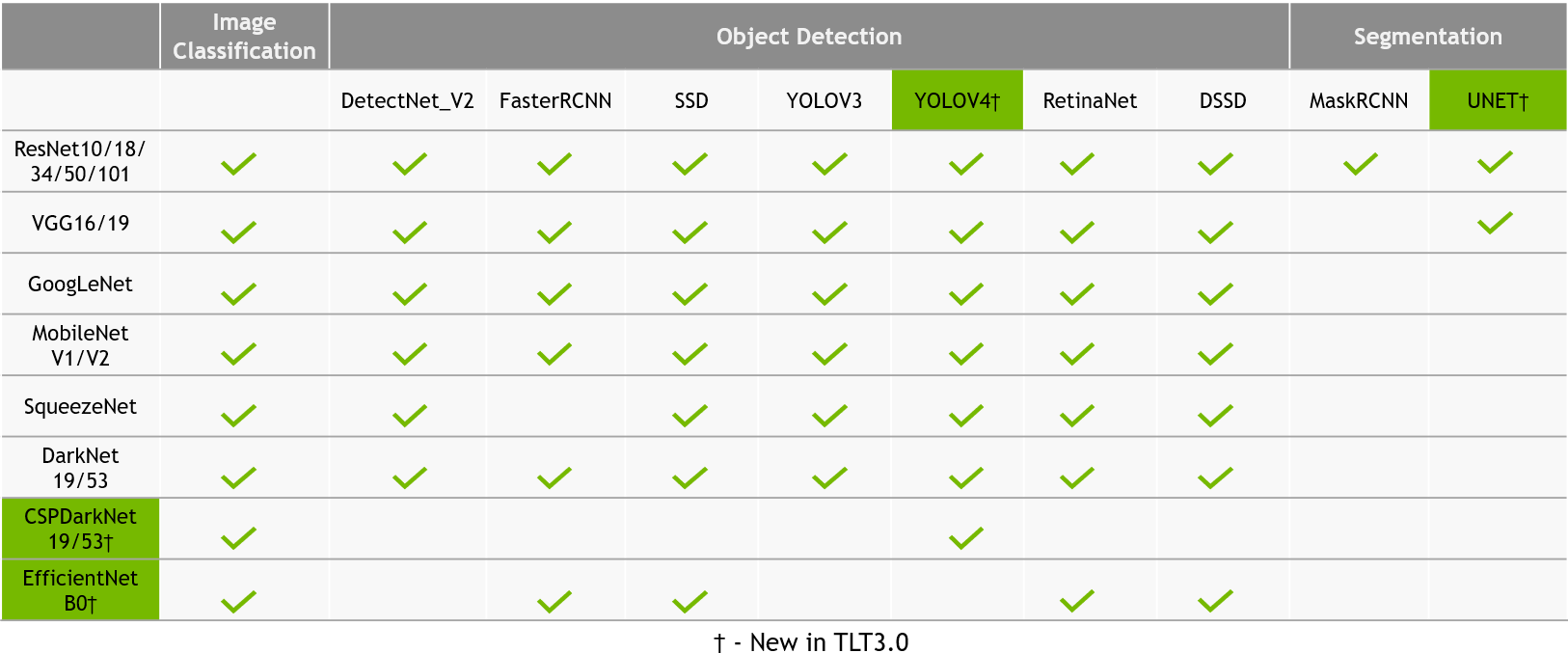
TAO Toolkit Computer Vision Sample Workflows NVIDIA NGC
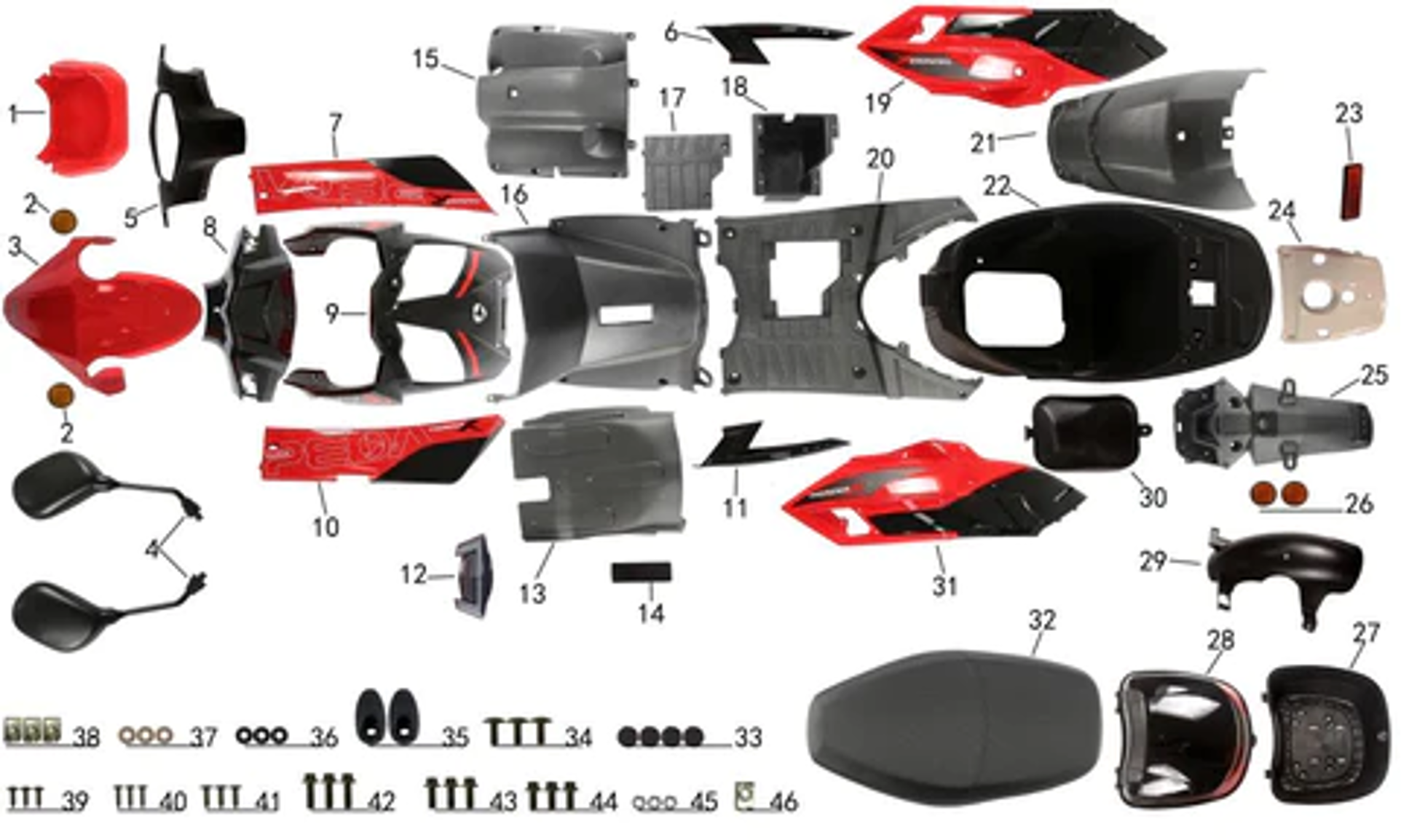
Tao Tao Parts VMC Chinese Parts in 2022 Go kart parts, Go kart
Hướng dẫn cách tạo catalog sản phẩm trong WordPress 2024
Tao Blade 50 Plastics
Bật mí cách tạo catalog trong lightroom đơn giản và hiệu quả cho bạn
Hướng dẫn cách tạo catalog sản phẩm trong WordPress 2024
Van Tao Catalog thomasjan.vn Page 1 5 Flip PDF Online PubHTML5
It Includes The Capability To Intercept Shipments Of New Computer Equipment.
Der Spiegel’s Fairly Harrowing Report About The Nsa’s Hacking Unit, Tailored Access Operations (Tao), Got A Little More Harrowing This Morning When An Unnamed Blogger.
Discover A Wide Range Of Items Available For Purchase At Great Prices.
Der Spiegel Has Several Feature Articles This Week On The Nsa 'S Backdoor Program Tao, Which Stands For Tailored Access Operations. This Is The Nsa 'S Top Operative.
Related Post: